
June 29, 2020
Good morning, everyone!
Welcome to Cyber Security News & Tips for SMBs!
People often ask me why I don't have an email newsletter, and I usually reply "because I post so much on social media -- do you really want to read MORE of my stuff?" LOL But I understand that many people simply don't spend time on social media -- or they used to, but they are cutting back. So I'm going to give this email newsletter thing a try. Let's see how it goes!
A few times each month, I’ll be sending you short emails with hot news and good advice on developing your information security program. (If you don’t want any more emails from me, just say so and I’ll stop. But I think you’ll be missing out on important information!)
I’d love to hear your thoughts or questions in response! Unlike a website, email is inherently two-way, and I look forward to reading and responding to every reply.
Right now you are probably thinking “Well, okay, but "Information security program"? I’m only worried about cyber security.”
The first important concept I want you to understand is this: “cyber security is not just an IT problem.”
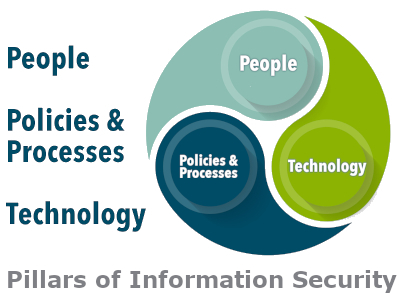
The three pillars of information security are:
- People
- Policies & Processes
- Technology
Did you notice that technology comes last?!?!?
There is no amount of technology you can throw at the problem of cyber crime to make it go away! If that were true, large corporations would never have data breaches – but they do.
It is impossible to achieve effective cyber security without (training) people to follow (written) policies and procedures when using technology. It takes all three pillars, in balance and cooperation, to be effective.
This is why policies and training comprise one of the five steps I’ve identified as the most important to maximize your cyber security investment.
If your employees sidestep the controls you have in place because they find them inconvenient and don’t understand the purpose, you have a cyber security weakness that can’t be fixed by buying another product or “solution.”
You can read more in my white paper "Five Steps to Maximize Your Investment in Cyber Security" available for download at https://theneteffect.com//download.php (In fact, you can access our complete whitepaper library from this form).
So the takeaway for today is to think of cyber security not as a standalone goal, but as part of your information security program.
Talk to you again soon!
PS - Please whitelist my email address or add me to your Contacts, to be sure my emails don't go to your spam folder!
PPS -- Check out my upcoming Work(fromhome)Shops!

Glenda R. Snodgrass
grs@theneteffect.com
(251) 433-0196 x107
https://www.theneteffect.com
For information security news & tips, follow me!

