March 2, 2021
Good morning, everyone!
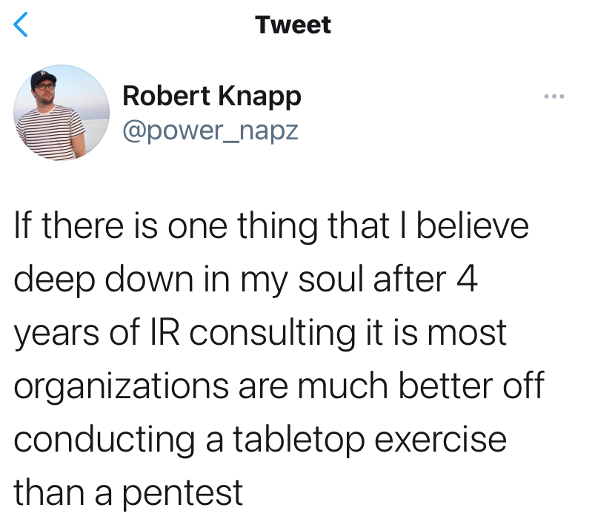 This recent tweet from Robert Knapp, an incident response (IR) consultant at Rapid 7, caught my attention. How many of you know
what a table top exercise is? Anyone? Anyone? Buehler? No? Well, let's talk about that today! This is something that can be useful at home and at work.
This recent tweet from Robert Knapp, an incident response (IR) consultant at Rapid 7, caught my attention. How many of you know
what a table top exercise is? Anyone? Anyone? Buehler? No? Well, let's talk about that today! This is something that can be useful at home and at work.
Wikipedia tells us that table top exercises (TTX) originated as a simulated form of military exercise:
A subset of simulated exercises is the Table Top Exercise (TTX), typically limited to senior personnel stepping through the decision-making processes they would employ in a crisis, a contingency, or general warfare.
TTX are a great way to find gaps in your disaster preparation plans! They can be used to simulate any kind of disaster:
- physical disasters like hurricanes, tornadoes, snow storms
- operational disasters like power outages, major equipment failures, computer/network failures, supply chain problems
- cyber disasters like ransomware, business email compromise, web/cloud services going offline, loss of Internet access
- personal disasters like an auto accident, the loss of a family member, a house fire
So how does it work? Brain storm scenarios, what kind of things could possibly happen. Here are a few ideas to get you started:
- The spare front door key was given to a temporary worker who put it in an envelope with the address and the alarm code written on it, and now he can’t find it.
- A company responsible for a critical part of your business data has informed you of a breach.
- A client calls and accuses you of having suffered a breach.
- Your domain registrar has suspended your primary domain. It is not immediately responsive to basic support inquiries. Your website is down. No new online sales, and you can’t process the ones that were made earlier.
- Your office building was robbed over the weekend. All computers were stolen. And the safe.
- Your IT vendor has had their TeamViewer account hacked and attackers have console access to your server.
- Your cloud backup sends you an email that you have successfully changed the encryption key to your backups. But you didn’t.
- Your cloud-based ERP/CRM/accounting system is down and you can’t get anyone there on the phone. There’s nothing in the news.
So what is the plan? Who is responsible? What do they do?
Who needs to be at the table for the exercises? Operations, finance, IT, security, legal, communications … ? Remember, you not only have to deal with the disaster itself, but the fallout from the disaster, which may have legal and PR implications.
Give some thought to things that you need to have in place BEFORE disaster strikes. Like a phone tree (and backup copy of master contacts list) to contact family members/employees/customers/vendors when urgent communication is needed.
|
Firefox has released a new version of its web browser with Enhanced Tracking Protection: Enhanced Tracking Protection in Firefox automatically protects your privacy while you browse. It blocks many of the trackers that follow you around online to collect information about your browsing habits and interests. It also includes protections against harmful scripts, such as malware that drains your battery. |
I think that's enough for this week. Go forth and apply your patches, enable 2FA and think before you click!
Remember, you can read past editions of this newsletter on our website, along with tons more information under the Resources tab.
Talk to you again soon!

Glenda R. Snodgrass
grs@theneteffect.com
(251) 433-0196 x107
https://www.theneteffect.com
For information security news & tips, follow me!
Security Awareness Training Goes Virtual
Thanks to COVID-19, lots of things are going virtual, and that includes my employee Security Awareness Training. I've set up
a small studio in our conference room (nobody there but me) so I can provide live training (almost) just like before!
You can see me wave my hands and make faces while a wall of fascinating facts and practical tips slideshow across your screens, wherever
you and your employees may be.
Contact me to schedule your employee training sessions. They're fun! ☺
Contact
|
The Net Effect, L.L.C.
|
Resources
|
CMMC Newsletter Whitepapers Articles Videos Interviews |

